PayPal Inc - Mobile API vulnerable to restriction Auth Bypass Issue
PayPal Inc - Mobile API vulnerable to restriction Auth Bypass Issue
This week the vulnerability laboratory disclosed an issue in the mobile api of the paypal ios application. The issue allows remote attackers to bypass the account restriction mechanism that blocks malicious or illegal acting users.
The security vulnerability is located in the mobile api auth procedure of the paypal online-service. The mobile app api does not check for already restricted/blocked application accounts. Remote attackers are able to login through the mobile api with paypal portal restriction to access account information or interact with the compromised account.
If a paypal user tries several times to login with a wrong password/user combination the paypal account will temporarily be closed for security reasons. When this happens the user needs to answer a secret question to get the account open again. Even if the account is temporarily closed it is possible to get access to the account via the paypal mobile app client through the API.
The client API checks only if the account exists, the API does not check a part- or full blocking of the account. It is possible for the blocked user to get access to his paypal account and is able to make transactions and he can send money from the account. The mobile iPhone / iPad Paypal App does need a security upgrade to ensure that the status of an account is also verified and how the App reacts when such an event takes place. This would ensure that no one can have access via the mobile client to a blocked account. In the Paypal database there are several preferences for an account to verify the status of the account. These preferences need to be used to check also the account status on the mobile client API. There is another exception which drops a push message on iOS devices (iphone & ipad) which refers to the main paypal website but it is only a temporary solution and no possibility to block account stable.
During the pentest the researcher revealed that he was able to access the blocked test account through the mobile application api. At the end the researcher was able to interact through the mobile app by easily accessing the information of the paypal account x01445@gmail.com.
The security risk of the auth bypass restriction vulnerability is estimated as high with a cvss (common vulnerability scoring system) count of 6.2. Exploitation of the vulnerability requires a restricted/blocked account of the paypal application without user interaction. Successful exploitation of the issue results in auth restriction bypass through the official mobile paypal app api.
Vulnerable Service(s):
[+] PayPal Inc
Vulnerable Software(s):
[+] PayPal iOS App (iPhone & iPad) v4.6.0
Vulnerable Module(s):
[+] API
Affected Module(s):
[+] Login Verification – (Auth)
Proof of Concept (PoC):
The auth bypass restriction vulnerability can be exploited by remote attackers without user interaction but with low privileged application user account. For security demonstration or to reproduce the vulnerability follow the provided information and steps below to continue.
Site: PayPal Inc (www.paypal.com)
Test Account: x01445@gmail.com 01x445@gmail.com
Mobile Client: https://itunes.apple.com/us/app/paypal/id283646709
#1 Manual steps to reproduce the issue with security question
1. Register a regular PayPal account linked to a banking account
2. Go to the login & provoke the ask for security questions after several wrong forced passwords login requests
3. It is also possible to do it when logged into the account and provoke via transaction cancels & co.
4. Now, try to login again and we see the "Security Question" module
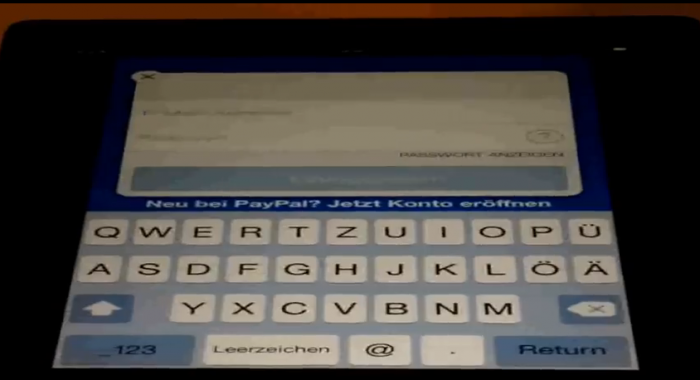
5. We switch to our iphone or ipad device and download & install the new paypal mobile application v4.6.0
6. Open the mobile application on your ipad or iphone device and login to your account
Note: The security protection mechanism of the main paypal core application disallows to login
without the verification attempt of the security question module!
7. The application allows the user to login via the mobile paypal app api without auth cancel or sec question popup
8. We login successful!
9. Now, the attacker can handle transactions, send money, request money, add funds, change address or include new cards
10. Successful reproduced!
#2 Manual steps to reproduce the issue without security question
1. Install the application to your iOS device (ipad or iphone)
2. Register a paypal inc user account
3. Solve a transaction and provoke an incident that the account get blocked
4. Now, login to the ios device and start the paypal application
5. Include the blocked login credentials and press the login button
6. The service grants access through the mobile api without processing to drop any exception to prevent the access
Note: Now the attacker is able to request the stored data of the paypal user in the portal even if the
service is restricted accessable. Regular the service must block you like when you login to the portal
but in case of the issue the api grants the access because of missing value check.
Security Video Demonstration Description
The video shows two blocked accounts. The first is the 01x445@gmail.com pp test account and the second is the x01445@gmail.com pp test account. The first one is nulled and frozen and the second one has also been blocked. The video shows in the first steps both login profiles with are unsuccessful. After providing to demonstrate that the x01445@gmail.com account is not allowed to access the portal we show how to unauthorized access the account information even if the service has blocked to login through the main paypal. The researcher demonstrates how to bypass the restricted account to get access and interact via api.
Paypal Inc (Bug Bounty Program) 2014 - Account Restriction Auth Bypass Vulnerability (Mobile API)
Even if the issue has a real impact the paypal team has not rewarded the researcher benjamin kunz mejri for the advisory reports. In a statement ebay officials wrote back that the issue is not actionable and users account data is not affected. Yes, you heard right ... we also was a bit confused after this answer has been arrived. We will not start making people angry but we gona talk publicly about this problem very soon if the problem persists to us and other researchers.
Advisory: http://www.vulnerability-lab.com/get_content.php?id=895
Video: http://www.vulnerability-lab.com/get_content.php?id=1338
Reference(s):
http://www.techworm.net/2014/10/flaw-in-paypal-authentication.html
Reference(s): Articles
http://www.securityweek.com/paypal-mobile-api-flaw-allows-security-feature-bypass
http://sensorstechforum.com/de/paypal-authentication-process-flaw-makes-blocked-accounts-accessible/
http://www.techworm.net/2014/10/flaw-in-paypal-authentication.html
http://thehackernews.com/2014/10/authentication-flaw-in-paypal-mobile.html
http://securityaffairs.co/wordpress/29104/hacking/authentication-vulnerability-paypal-mobile.html
http://hackingpost.com/authentication-flaw-paypal-mobile-api-allows-access-blocked-accounts/
UPDATE: 2014-10-14
Today ebay officials wrote in a statement to the vulnerability laboratory that the vulnerability that has been disclosed will be patched during the next update periods and that the researcher will receive a reward for keeping the paypal inc services/site secure. During a revisit of the issue ticket the analysts of the issue has decided to reward the researcher because the issue does match the scope of the program. We would like to say acknowledge the ebay inc team for coordination+reward and paypal inc for accepting the zeroday auth bypass vulnerability. Thanks to SecurityNews, Softpedia, SecurityWeek, Forbes Magazine, SC Business Intelligence News, TheHackerNews and SecurityAffairs.



Comments
Yang S
genius
Evan Akhtar
Add new comment